In today’s swiftly evolving technological landscape, the proactive identification of anomalies within expansive datasets has emerged as a crucial focal point for organizations committed to enhancing their cybersecurity protocols. SureLog features a highly advanced UEBA module.
While SureLog prides itself on its own machine learning (ML) detection model, its open architecture and provision of historical logs spanning multiple years offer a novel avenue for Security Operations Center (SOC) analysts. SureLog, fortified with a robust big data infrastructure, stands out as a formidable ally in this pursuit.
This amalgamation of SureLog’s data reservoir and its open architecture not only augments the capabilities of security analysts but also broadens the scope for leveraging machine learning models to bolster anomaly detection. By providing extensive logs of past activities, SureLog facilitates the creation of enriched datasets, enabling more accurate anomaly identification and deeper insights into potential security threats.
Moreover, while SureLog’s inherent ML detection model provides a foundation for anomaly detection, the integration of artificial intelligence, particularly through the innovative utilization of AI-powered chatbots like FormulaBot, propels the efficiency and precision of this process to new heights. FormulaBot serves as an indispensable assistant, streamlining the analysis of vast volumes of data and enabling swift identification and resolution of anomalies.
Here’s an in-depth guide detailing how to optimize SureLog’s capabilities alongside FormulaBot, specifically designed to efficiently detect and address anomalies:
1. Leveraging SureLog’s Open Access API and Hot Data Lake
SureLog, with its capability to retain logs for at least a year within its hot data lake, provides a treasure trove of data for analysis. Enabling secure open access via API allows seamless interaction with this repository of valuable information.
2. Utilizing SureLog SIEM for Analytical Purposes
SureLog’s Security Information and Event Management (SIEM) system maintains logs for a substantial period, ensuring a wealth of data availability for analytical processes.
3. Harnessing FormulaBot’s AI Data Analyst Features
FormulaBot, an AI-powered chatbot, acts as a sophisticated data analyst. Leveraging its capabilities, organizations can automate anomaly detection processes and extract meaningful insights from the vast datasets stored in SureLog.
4. Connecting FormulaBot to SureLog
Initiate the connection between FormulaBot and SureLog to enable seamless communication and data retrieval for subsequent analysis.
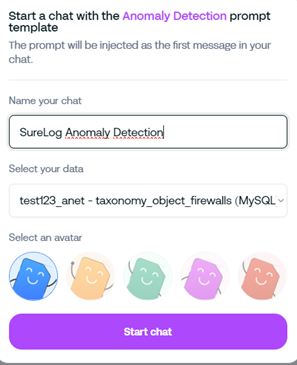
5. Implementing Anomaly Detection Using FormulaBot
Prompt for Anomaly Detection: “Implement anomaly detection on the SureLog dataset following these instructions:
Data Preprocessing: Normalize the dataset to ensure uniformity and consistency.
Isolation Forest Method: Utilize the Isolation Forest anomaly detection method to identify outliers.
Applying the Method: Apply the Isolation Forest method to the dataset to detect anomalies.
Creating an Anomaly Identification Column: Generate a new column in the original dataframe to denote whether an observation is an anomaly or not.
Conclusion
By seamlessly integrating SureLog’s rich data repository with the analytical prowess of AI-driven chatbots like FormulaBot, organizations can streamline anomaly detection processes and bolster their cybersecurity posture. This synergy between cutting-edge technologies not only enables efficient anomaly identification but also facilitates proactive mitigation strategies, safeguarding against potential threats within the network.
The marriage of SureLog’s comprehensive log retention capabilities and FormulaBot’s AI-driven analytical functionalities represents a promising frontier in the realm of anomaly detection, empowering organizations to stay ahead in the ever-evolving landscape of cybersecurity.
For more information on leveraging SureLog and AI-driven analytics for anomaly detection or cybersecurity best practices, feel free to get in touch with our experts.
Stay secure, stay vigilant.





