Event correlation techniques are designed to detect events, make sense of them and assign the appropriate control action. As data becomes more complex, the need for correlation intelligence will continue to increase in significance.
SureLog SIEM correlation engine has many advanced features. One of them is “Never Seen Before” type of rules.
This type of rules starts to collect values immediately. Collects values during the learning phase and then monitor for any value that has not seen before.
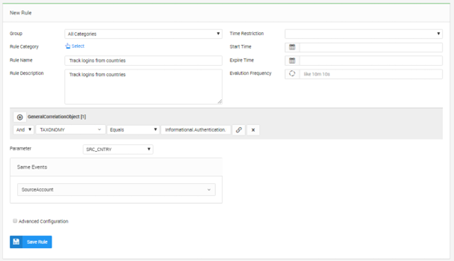
Sample rule 1:
This rule will track logins from countries on a per user basis, baselining log in countries for the past 30 days. Once a user authenticates from a location not seen in that period, the rule will trigger.
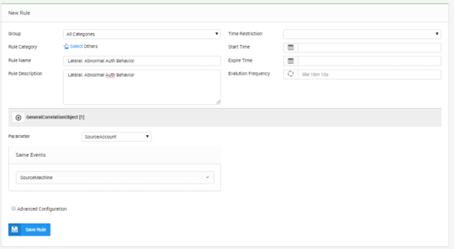
Sample rule 2: Lateral: Abnormal Auth Behavior
This rule first tracks which hosts an account typically authenticates to. Afterwards, triggers when a new host or hosts are being accessed by the account.
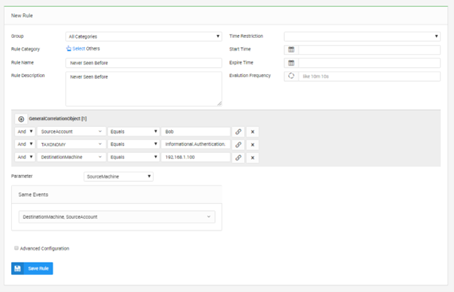
Sample rule 3:
If Bob’s authantition activity to 192.168.1.100 has a SourceMachine value never seen before , notify (Monitor SourceMachine value for new data (Never Seen before data) for this SourceAccount and this DestinationMachine)
References
1. https://digitalguardian.com/blog/what-event-correlation-examples-benefits-and-more