“Every Journey starts with a single step”
A SIEM Security Use Case is this first single step in the, increasingly more important, task of identifying threats in our corporate environment.
This article may interest you
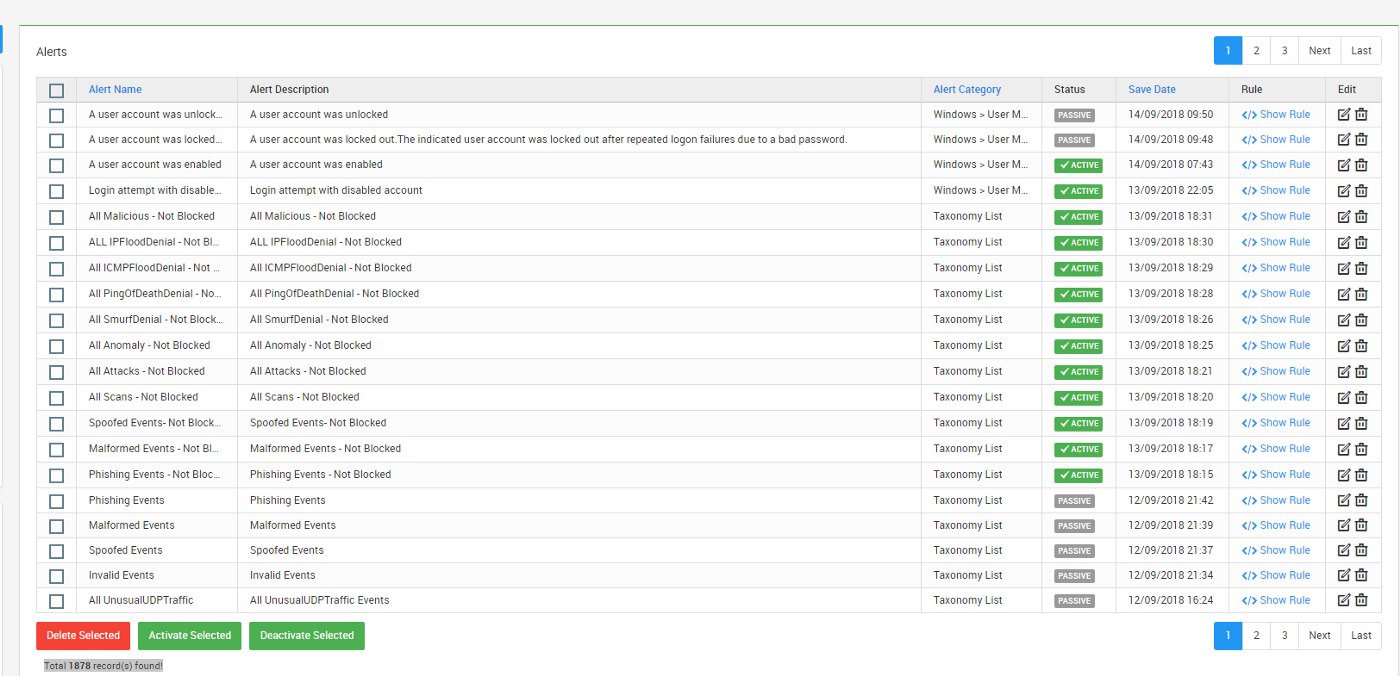
SureLog SIEM built in 1800+ use cases includes:
- A process start and the files accessed by this process within 15 minutes on the same machine is a process-file access pattern. And if this pattern is seen more than 2 machines within 20 minutes, then notify.
- A corporate user downloaded a suspicious file at home and got infected. Now the attacker has gained access to her machine.Days later at work, suspicious C&C activity is detected originating from the same user machine. A week later, the attacker uses the same user’s credentials to escalate her privileges. A few days after that, the attacker uses her improved privileges and credentials to download a treasure trove of sensitive information. A few days after that the attacker manages to exfiltrate the data to a server in one of Suspicious Countries.
- Check If a request was blocked via waf from an IP address. Then check WEB Server (IIS, etc..) logs if there is a block action to a request from the same IP address was seen within 2 minutes.
- Check if there is Powershell User-Agent (WindowsPowerShell) in proxy logs.
- A user switches from their normal account to a privileged one then performs an abnormal data transfer to suspicious countries.
- A user VPNs to the network from a new location for the first time, then accesses a shared file system.
- A user logs in remotely at 3 midnight, then makes repeated attempts to connect to a production database as an administrator.
The content has been sourced from




